Google has quietly resubmitted a disclosure of a critical code-execution vulnerability affecting thousands of individual apps and software frameworks after its previous submission left readers with the mistaken impression that the threat affected only the Chrome browser.
The vulnerability originates in the libwebp code library, which Google created in 2010 for rendering images in webp, a then-new format that resulted in files that were up to 26 percent smaller than PNG images. Libwebp is incorporated into just about every app, operating system, or other code library that renders webp images, most notably the Electron framework used in Chrome and many other apps that run on both desktop and mobile devices.
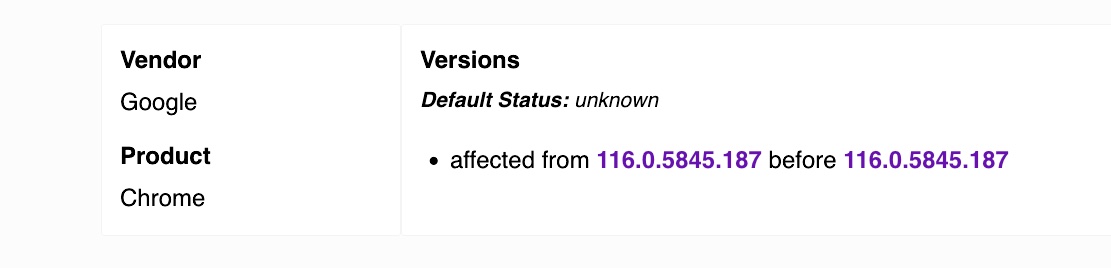
Two weeks ago, Google issued a security advisory for what it said was a heap buffer overflow in WebP in Chrome. Google’s formal description, tracked as CVE-2023-4863, scoped the affected vendor as “Google” and the software affected as “Chrome,” even though any code that used libwebp was vulnerable. Critics warned that Google’s failure to note that thousands of other pieces of code were also vulnerable would result in unnecessary delays in patching the vulnerability, which allows attackers to execute malicious code when users do nothing more than view a booby-trapped webp image.
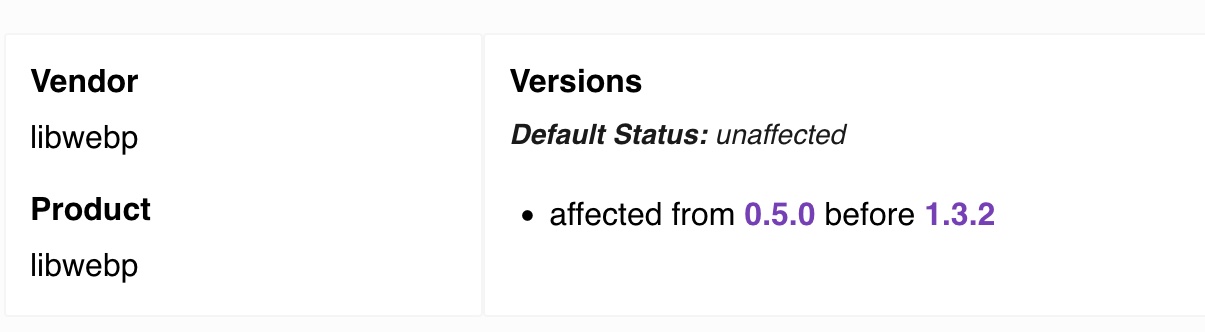
On Monday, Google submitted a new disclosure that’s tracked as CVE-2023-5129. The new entry correctly lists libwebp as the affected vendor and affected software. It also bumps up the severity rating of the vulnerability, from 8.8 out of a possible 10 to 10.



 Loading comments...
Loading comments...